Phishing – Don’t Take The Bait
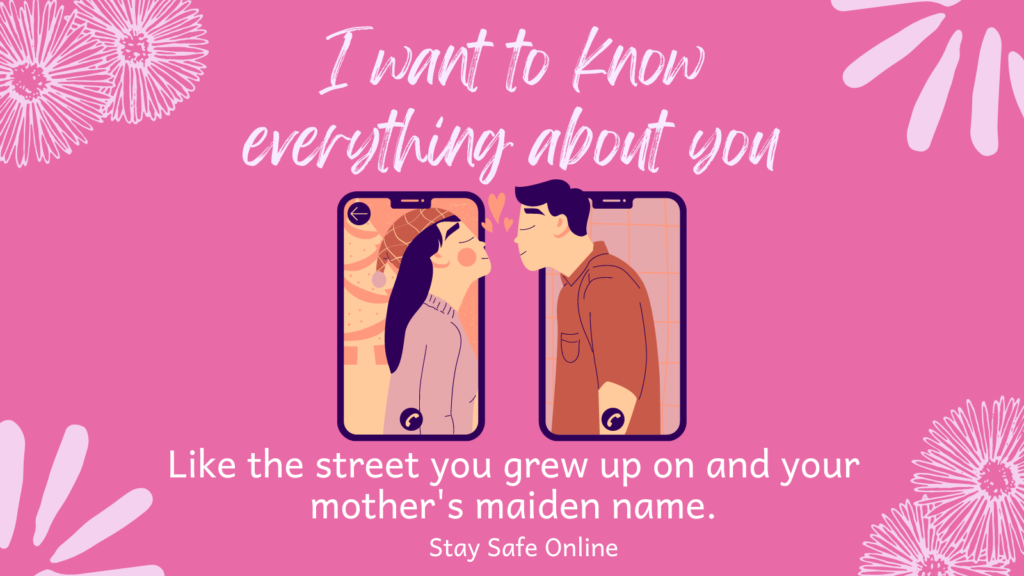
Can you spot the phish? One of the main ways cybercriminals steal funds and information or spread ransomware is by gathering information through phishing emails. Not all phishing emails are full of spelling errors and sent from people purporting to be Nigerian princes. Some are quite sophisticated, and emulate known and trusted brands. Try this […]
Phishing – Don’t Take The Bait Read More »